- 1password On Premise Page
- 1password On Premises
- 1password On Premise Id
- One Password On Premise
- 1password On Premise Meaning
In this video, you'll learn how to deploy password protection in your on-premise environment. Learn more: https://docs.microsoft.com/en-us/azure/active-direc. Though Microsoft historically has benefited from on-premise services, the success of Azure pivoted the company from on-premise. It is understandable why Microsoft wants everyone to migrate to cloud. But, cloud services are not all sunshine and rainbows. Organisations would like their data to stay with them. If this version is greater than or equal to 1.0.0419.0911, you can proceed configuring Self-Service Password Reset with On-Premise writeback. Otherwise, it is always good to upgrade your DirSync. As I told you in the beginning, change is inevitable.
Last year I wrote a blogpost on password in Azure Active Directory (Choose a password that’s harder for people to guess – https://jaapwesselius.com/2018/10/15/choose-a-password-thats-harder-for-people-to-guess/) in which I mentioned the banned password lists and the Azure AD Password Protect feature. Back then this was only for Azure AD, but right now it is also available for on-premises Domain Controller as well (for some time already). It is possible for on-premises Domain Controllers to use the password protect functionality in Azure AD and thus block the possibility to use weak passwords in your on-premises environment. Let’s see how it works.
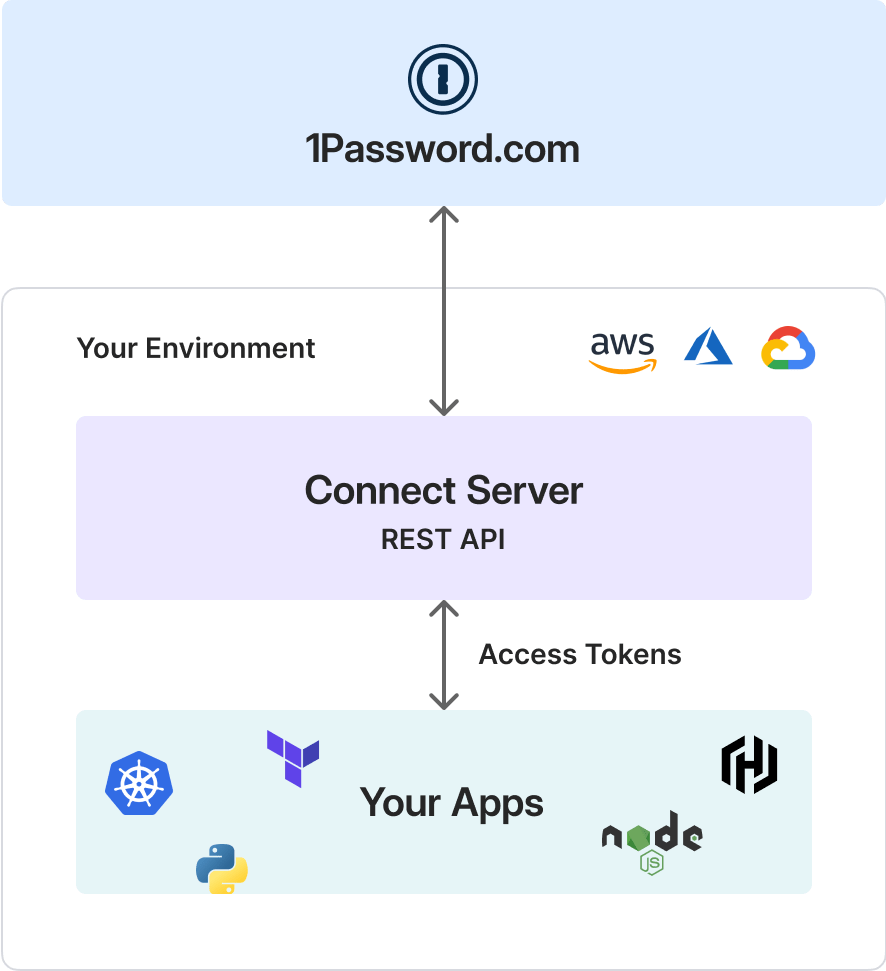
The password protection feature on-premises uses a Password Protection Agent that’s running on the on-premises Domain Controllers. When a user initiates a password change, the new password is validated by the Azure AD Password Protection agent, which request a password policy from the Azure AD Password Protection proxy service. This Password Protection service requests a password policy from Azure AD. The new password is never sent to Azure AD. This is shown in the following picture (borrowed from the Microsoft website):
After receiving the password policy, the agent returns pass or fail for the new password. In case of fail the user must try it again.
1password On Premise Page
Installation of the password protect consists of two steps:
- The Azure AD Password Protection Proxy service using the AzureADPasswordProtectionProxySetup.exe software installer. This is installed on a domain joined computer that has access to the Internet and proxies the password policy request to Azure Active Directory.
- The DC Agent service for password protection by using the AzureADPasswordProtectionDCAgentSetup.msi package. This runs on the Domain Controllers and send the password policy requests to the server running the proxy service.
Both can be downloaded from the Microsoft download center on https://www.microsoft.com/en-us/download/details.aspx?id=57071
Password Protection Proxy Installation
The first step is to install the password protection service. This server should be able to access Azure AD and since the Domain Controller does not have an internet connection this should be installed on a separate server. In my lab environment I have installed the password protection service on the Azure AD Connect server.
Installation of the password protection proxy is straightforward; you can use the GUI or the command line setup with the /quit switch for unattended install (and Server Core). After installation use PowerShell to register the proxy in Azure AD by using the following commands:
This command can work when you have MFA enabled for admin accounts, if you don’t require MFA on your admin accounts (which is a bad practice IMHO) you can use the following command:
The last step is to register the forest in Azure Active Directory. This is very similar to the registration process of the proxy service. You can use the following PowerShell commands to register the forest:
[PS] C:> Register-AzureADPasswordProtectionForest -AccountUpn ‘yourglobaladmin@yourtenant.onmicrosoft.com’
Again, when MFA is not enabled you can use the following command to register your forest in Azure AD:
Note. A multi-forest scenario is supported for the Password Protection service, you can install multiple forest using these commands. Multiple domains against one tenant is supported, one domain against multiple tenants is a not-supported scenario.
Some remarks:
- The server where the password proxy agent server is installed should have .NET Framework 4.7 or higher installed.
- For high availability it is recommended to install the password protection agents on multiple servers
- The password protection proxy supports an in-place upgrade, so a newer version can be installed without uninstalling the previous version.
So how does this work, and how does the password protection service find the proxy server (or servers)?
When the Password Protection Proxy is installed it is registered in Active Directory with a well-know GUID. The Password Protection Agent checks Active Directory for this well-know GUID and finds the server where the Password Protection Agent is installed.
You can use the following PowerShell commands to find the Password Protection Proxy:
It returns the server, and you can use ADSIEdit to inspect the computer:
1password On Premises
This is much like how domain-joined Outlook clients find the Autodiscover SCP in Active Directory.
1password On Premise Id
Installing the DC agent service
When the proxy service is installed and registered the Domain Controller agent service can be installed. It is just an MSI package that can be installed (using the GUI, accept license agreement and click install) or you can install it on the command line using the following command (use elevated privileges):
One Password On Premise
Note. Installation of the DC agent requires a restart, but you can use the /norestart switch to reboot at a more convenient time.

After rebooting the Domain Controller the password protection service is ready for use.
1password On Premise Meaning
Some remarks:
- Azure AD Password protection service requires an Azure AD Premium P1 or P2 license.
- Domain Controllers should be Windows 2012 or higher.
- Domain Controllers should have .NET Framework 4.5 or higher installed.
- You never know which Domain Controller is going to process a password change. Therefore, the Password Protection service need to be installed on all Domain Controllers. For a straightforward environment this should not be a problem, but for large enterprises with lots of DC’s it can be an issue (I deliberately do not that about security officers at this point :-))
- Both the proxy service and the DC agent support an in-place upgrade, so a newer version can be installed without uninstalling the old version.
Testing the Azure AD Password Protection service
So, after installing the Password Protection Proxy and the DC agent it’s time to test which is relatively simple. Logon to a domain-joined workstation, use CTRL-ALT-DELETE to change the password. When using a simple password like “Summer2019” or something it fails with the following error message.
From this moment on it is no longer possible to use weak passwords, locally enforced by Azure Active Directory and again a step closer to a safer environment.
